SessionGuardian Annual Threat Review - 2023

SessionGuardian announced that it is fully GDPR compliant after a compliance audit by Prescient Assurance.
Learn how to secure remote workers while respecting user privacy. Discover the benefits of GDPR-compliant solutions like SessionGuardian.
We have compiled our top 5 security recommendations to help you maintain an appropriate security posture in WFH and other remote document reviews.

Secure your hybrid workforces across VDI and browser workspaces while maintaining regulatory compliance with SessionGuardian. Learn why the combination of flexible work policies and remote work technology helps enterprises reduce attrition rates, increase productivity, and save thousands.
Discover how enterprises are saving up to $11k per employee with secure remote work.

Recognized by Gartner in the innovation trigger, SessionGuardian is a Sample Vendor in the Hype Cycle for Endpoint Security, 2022.

SessionGuardian, the leader in continuous identity verification for hybrid teams working with sensitive data, has been recognized in the Gartner Hype Cycle for Endpoint Security, 2022.
Learn more about SessionGuardian’s security solution that secures hybrid, distributed workforces while maintaining global regulatory compliance.
SessionGuardian, the leader in identity access control and authentication for hybrid teams working with highly sensitive data, today announced $3 million in seed funding.
Learn how SessionGuardian's security measures comply with industry-leading data privacy regulations such as Illinois' BIPA, California's CCPA and CPRA, the EU's GDPR, and Singapore's PDPA. This white paper discusses the importance of consent and data protection in user data and privacy. Stay compliant and secure with SessionGuardian.

Current research indicates the primary causes of data breaches are due to human error. To fight this, companies are trying to implement comprehensive security measures, but face issues with these measures conflicting with user data privacy. This whitepaper details how SessionGuardian's security protocols adhere to data privacy regulations including Illinois' BIPA, California's CCPA and CPRA, the EU's GDPR, and Singapore's PDPA.

Learn how to effectively implement physical security controls in a hybrid environment. This white paper discusses the challenges and solutions for protecting both on-premises and remote employees. Discover the benefits of a comprehensive security strategy for your organization.

Discover how continuous authentication can improve security and user experience for your organization in this comprehensive white paper. Learn about the latest technology and best practices for implementing continuous authentication in your systems.
In this podcast interview session, the speakers discussed some challenges and solutions when implementing security in a hybrid/remote environment.
Enabling Physical Security Controls in a Hybrid Environment discusses the advancement in software solutions that would allow hybrid working without losing the controls associated with a secure room environment—and without sacrificing regulatory compliance.



In a landmark achievement for SessionGuardian, our Continuous Identity Verification technology has been verified as Citrix Ready® and is part of the Citrix Ready Workspace Security initiative.

SessionGuardian, the global leader in continuous identity verification, announced the launch of its new product, SessionGuardian Browser.

SessionGuardian, the global leader in continuous identity verification, announced that its cybersecurity software that protects against data theft, has been verified as Citrix Ready.

SessionGuardian, the global leader in continuous identity verification, welcomes two new experts in financial services cybersecurity to the team.

SessionGuardian, an industry leader in endpoint security for distributed workforces, announced today that Rob Smith, former Gartner analyst, has joined the company’s advisory board.
SessionGuardian, the pioneer of the world’s first and only continuous identity verification software, has been recognized in the latest Gartner Hype Cycle for Endpoint Security, 2021

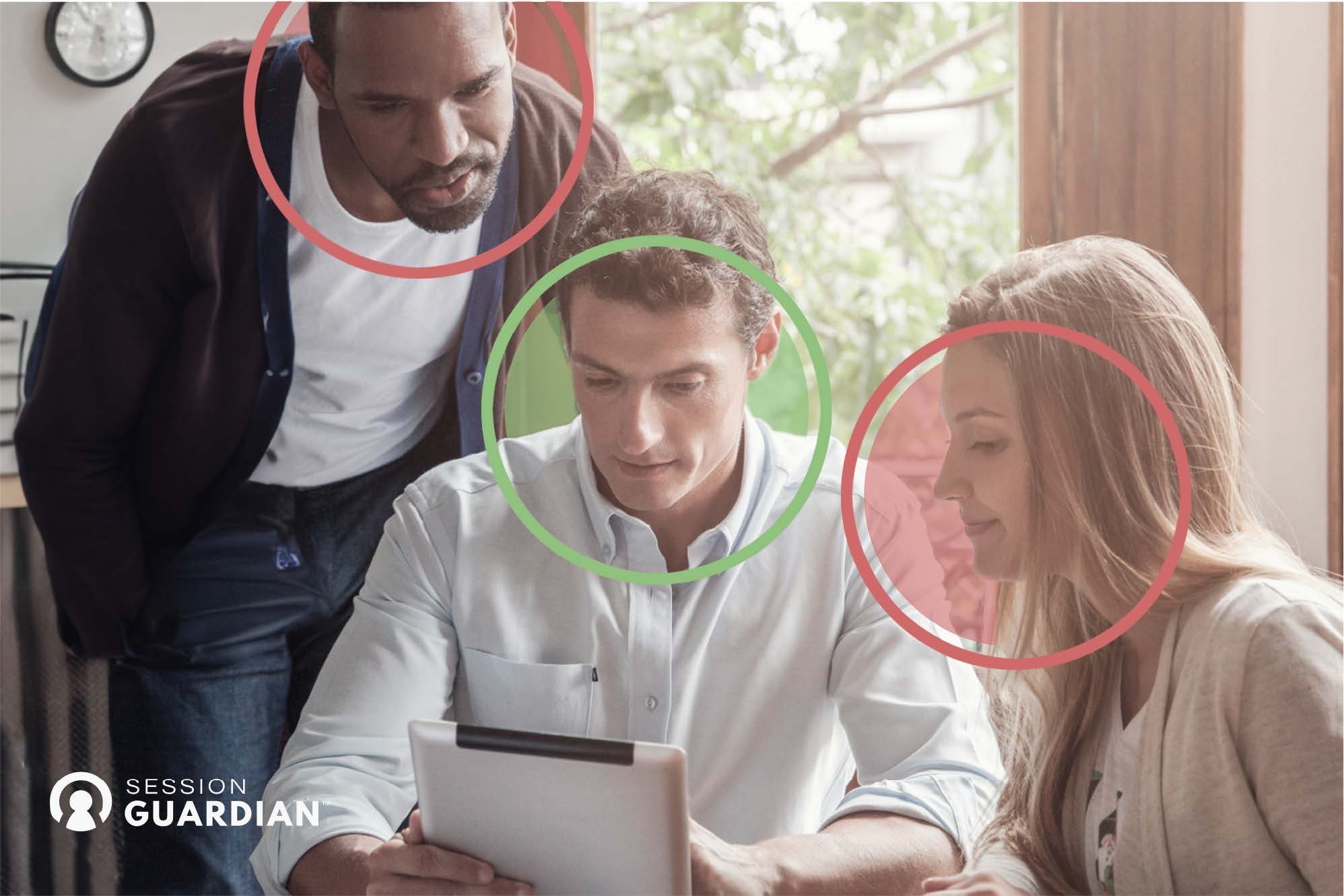
Zero Trust utilizes the principle of least privilege to ensure that access is given based on the unique functions of an individual’s role in a system.

Leading security companies like SessionGuardian were designed to address the critical gap caused by human behaviors.
.jpg)
Traditional VDI and DaaS security has been losing the battle against inside and outside threats, and in this new work-from-anywhere world the stakes have never been higher.
BYOD users are the most vulnerable to accidentally exposing data to outside threats and increasingly sophisticated attacks.

SecureReview, an industry leader in cybersecurity for distributed workforces, announced that they are debuting a new brand name and brand identity.
.jpg)
Don't play a guessing game with cybersecurity. Reduce your risk of information loss or security breach with SessionGuardian.

Though vastly different in scope and setting, each of these attacks on FinTech institutions could have been prevented by one thing: better security infrastructure.

WFH Cybersecurity Risk Management from Legal, Business and IT perspectives.

Remote work is a fact of life. COVID-19 restrictions increase #WFH security risks.

Companies no longer able to move data between EU and the US can now set up secure EU/UK platform to align with privacy controls.

With remote work on the rise, global reviews get next-gen security.

Secure Remote Review is a Game Changer for Virtual Workstation Security.

Integreon mobilized to create a comprehensive WFH solution that meets its clients’ rigorous standards.

SessionGuardian can help reduce Coronavirus-related business disruptions by enabling staff from corporations, law firms and service providers to continue working remotely on sensitive projects while maintaining a strong security posture.

The post-vaccine future is most likely to bring a hybrid of remote and on-premises work.

Get up to speed on the latest cybersecurity news and the current state and future outlook of cybersecurity in numbers.

COVID-19 left hospitals less resourced and more vulnerable than most Americans have seen in their lifetimes.

When we think about information security and data loss prevention tools, it is important to maintain a balance between collaboration and security.

The need for cybersecurity has existed since the dawn of the personal computer, and the pandemic has brought about a heightened awareness of document and data safety.

One of the biggest data breaches in history occurred with the SolarWinds hack.

The consequences of cyber attacks are particularly high in life sciences, with confidential patient and company data at risk.

It’s not enough to blindly trust WFH employees with sensitive company data. In the era of coronavirus, data leaks are up, while few, if any, files are properly protected.

Do you know who’s looking at your documents? Boost your security protocols with SessionGuardian.

Comply with discovery obligations while diligently protecting your client’s valuable IP, and do so cost effectively with a proven service provider to AMLAW 100 firms.

Due diligence can be a major undertaking, and a critical project toward a successful deal.

Enjoy an interesting conversation on the topic of WFH cybersecurity from multiple perspectives.

While COVID-19-driven office closures are taking their toll, some aspects of this crisis may actually be beneficial for business.

Enhanced data management means greater security for domestic & international corporations.
Learn to navigate the remote review landscape. Legal Operators hosts a webinar this week.

Like most organizations, your workforce has shifted from the office to remote work from home.

Global organizations are implementing 14-day quarantine, or “quarantine at home” procedures for staff who have traveled to areas affected by the Coronavirus.

There are so many ways that SessionGuardian helps reduce the risk of information disclosures on an upcoming project. Recently, SessionGuardian’s Jordan Ellington had an opportunity to converse with a customer (at a firm that’s ranked in the Am Law 50), and they touched on the most pressing concerns raised with specific product features.

Internal investigations that are necessary and appropriate to get at the facts involve the collection, analysis, and review of thousands, perhaps tens of thousands of sensitive emails and documents.

Sharing confidential documents is a necessary aspect of doing business. But conventional methods of sharing private matters also carries a degree of risk.

Wouldn’t it be great if your document review attorneys could access the docs from the office only if you choose — and only if the attorney’s face has been authenticated in front of the computer? That ideal state is available right now.

The powerful alchemy of AI and magic mojo of machine learning has not put document review attorneys across the globe out of business just yet.

When you regularly handle confidential documents, it’s an excellent idea to conduct information security audits. An information security audit is a great way to measure and assess the effectiveness of your security policies.
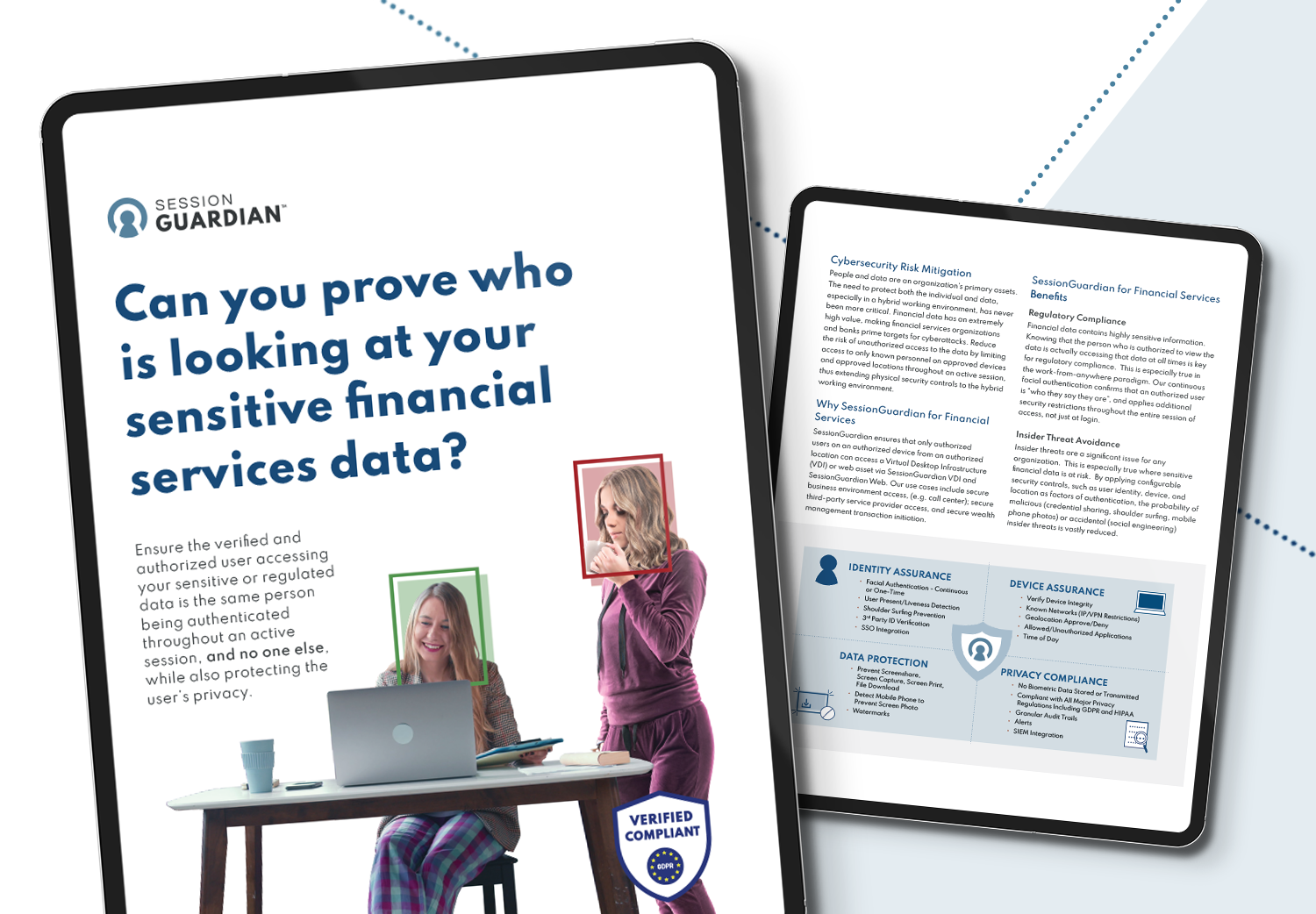
Can you prove who is looking at your sensitive financial services data?

.jpg)